The bug bounty approach means opening yourself up to being attacked in order to better defend yourself. This American cybersecurity proactive method is not new and dates back to the sixties. But it is now becoming established in Europe and particularly in France which today counts 2 bug bounty platforms that are among the most promising cybersecurity solutions worldwide. We met with them during the Cybersecurity Conference “Les Assises de la Cybersécurité” to find out more about their service.
Companies are exposed to an increasing number and variety of cyber threats. This trend has been accelerated with the digital transformation and COVID-19 crisis. Faced with these threats, cyber defense must renew itself and imagine new ways to counter these invisible attacks. Enter the bug bounty approach.
The idea is to call on the hacker community to test cybersecurity. If the hackers find vulnerabilities in a system, they are paid in the form of a bounty. Like bounty hunters in the American Wild West in the 19th century.
“Making the World a Safer Place”

This approach is widespread in the US. The Pentagon even opened its own platform, Hack the Pentagon, in 2016. And the market is developing. In 2020, according to bug bounty operator HackerOne, ethical hackers made $40 million overall in bounty.
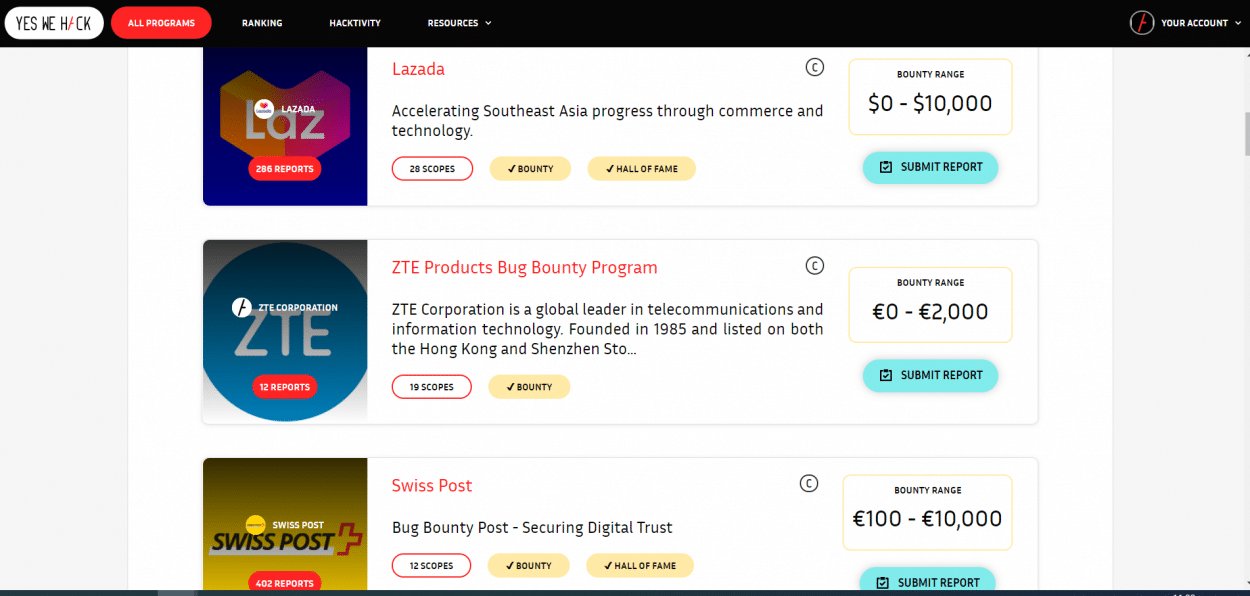
The American phenomenon is finding more and more echoes in Europe, specifically in France. Two platforms emerged in 2015: Yogosha and YesWeHack.
The American phenomenon is finding more and more echoes in Europe, specifically in France. Two platforms emerged in 2015: Yogosha and YesWeHack.
Fanny Forgeau, the CEO of Yogosha, describes her platform:
“Yogosha is a collaborative cybersecurity Saas platform accessible online where we allow our clients to work with ethical hackers that we select based on several criteria, so that they can identify security flaws and vulnerabilities in our clients’ systems. They report them so that they can be treated and fixed before criminals can exploit them. “Hacker” does not mean “criminal”. A hacker is basically a computer tinkerer, someone who fixes things and, in this case, aims to make the world a safer place.”
According to Guillaume Vassault-Houlière, Co-Founder of YesWeHack:
“Our model is based on this American model. We have a community of 30,000 hackers in 150 countries which allows for continuous and recurring testing to respond to new and evolving threats. We also have a pool of researchers who are always present and able to respond to all our customers, 24/7. Hacking is part of our values and daily life.”
How Does it Work?
The bug bounty process is simple. A company registers on a platform with a clear perimeter to be tested, whether it is a production line, mobile application or connected object.
Engineers of the platform study the request and the criticality of the perimeter and make the company a suitable offer with the price of the bounty. Both parties sign a contract on the platform which provides a level of legal protection. Once the bug bounty program has been set up, the freelance hacker who accepts the mission starts testing the different entry points to the determined perimeter. The first flaws can appear within a few hours. The hacker must then send in a comprehensive report to the company with the results of his/her testing before being rewarded.
Customers pay a subscription to access the platform and its services. This starts at a few thousand euros per year and can go up to several hundred thousand euros per year. Customers must also pay the hacker his/her bounty separately.
Fanny Forgeau from Yogosha explains:
“The client only pays the hacker if he judges that his report is relevant. At the beginning of the program, the client deposits an amount in a third-party escrow account on Mangopay. When the customer validates the report, part of the amount goes to the hacker. Yogosha does not benefit from the transaction but the platform is there to secure and determine upstream with the customer the amount of the bonus. The customer pays the hacker directly, not Yogosha.”
The customer can choose his/her hacker, based on his/her online profile (language(s), technical knowledge, ranking, etc.) and even his/her nationality explains Fanny:
“In France, in some strategic sectors, clients may ask to work only with French hackers.”
What are the Flaws?

According to Guillaume Vassault-Houlière from YesWeHack:
“Data leakage and GDPR compliance are among the top risks on the platform and this is where the bounty is the highest, between €200,000 and €230,000 depending on the criticality of the mission.”
Interconnection problems in the cloud, as well as the implementation and interoperability with different products, are also part of the common and usual flaws.
For Mrs. Forgeau,
“There is also the concern, for e-commerce players, of having a vulnerability that allows criminals to order for example 50 washing machines and only pay for one. These flaws are very common.”
Who Resorts to Bug Bounty?
Banks, insurance companies, e-commerce players, industrialists and public institutions (ministries, communities) are among the clients of both platforms.
Fanny explains:
“Software editors also come to test their solutions to prove that their systems are completely safe. Start-ups who need to be compliant before serving large groups also use the platform.”
Mr. Vassault-Houlière adds:
“We also have companies in the cybersecurity sector. It is good to develop tools that protect customers but they also have to be secure!”
YesWeHack boasts that its clients include French unicorns such as Doctolib, Dailymotion and Deezer as well as FT120 start-ups. Guillaume adds:
“During the COVID crisis, Doctolib intensified teleconsultations and accelerated development to bring out a product very quickly. They came to us to make sure that their systems were safe and flawless before releasing them to the public.”
How to Ensure the Hackers are Trustworthy?
Both platforms guarantee trustworthy hackers by implementing a rigorous recruitment process. First, they must take a technical test to find well-hidden flaws such as Dojo. Yogosha says the success rate of this test is 15 to 20%.
Then a trusted third party verifies the integrity of the hacker. Both platforms use Mangopay which does a KYC (know your customer) check to verify the identity of the hacker as well as his/her tax situation and address. For critical sectors involving public organizations, the hacker may undergo a criminal record check.

Mr. Vassault-Houlière explains:
“Unlike American platforms, at YesWeHack we check the identity of all the hackers registered on the platform with a focus on money traceability, anti-terrorism and money laundering as if we were opening a bank account in Europe. Hackers come from all over the world and they are subject to the RGPD. The submission to European legislation is a strength for us because it lends confidence to our model.”
Even if they don’t always physically meet their hackers, Yogosha and YesWe Hack assure us that their hackers are never anonymous. Mr. Vassault-Houlière also believes they cannot play a double game either.
“Our hackers are independent workers, they can work on several platforms. And we must not forget that the hacking environment is a trusted environment and there is a reputational issue.”
And for Mrs. Forgeau, even if it may seem strange to be voluntarily attacked to better defend oneself, it’s worth it in the end:
“Big bounty dates back to the ’60s. We now have enough use cases in France, in Europe and in the US to prove that it is effective. But there is still a lot of ignorance and fear.”
What Happens After a Security Breach is Discovered?
This is where things get a bit muddier. Platforms are there to help detect vulnerabilities, but what happens afterward?
Mr. Vassault-Houlière told us:
“We only do the detection of vulnerabilities and not the remediation. You can’t be judge and jury.”
This means that if a flaw is found on an editor program or application by the hacker, the platform and the hacker will have no guarantee that the editor in question will fix this flaw.
Some vendors may be reluctant to repair flaws in their programs when they are deemed to be of little importance and costly or difficult to fix.
There is also another issue with the bug bounty process. Hackers must stick to their mission of testing and not report any information they might receive from an outside source, which isn’t uncommon as the hacker community is very close-knit and information is often shared. They cannot report information they are led to be aware of without being mandated under penalty of losing their bonus.
For Fanny Forgeau,
“We never test unless we are asked to.”
As a result, many flaws are left unfixed until a publisher takes action or an attack takes place via the said flaw.
Furthermore, the fact that a hacker is reporting information about a vulnerability could backfire. He could himself be sued by the vendor for putting the company in jeopardy of cybercriminals.
Fanny Forgeau minimizes this risk. She confirms that the hackers can report flaws to them and they will then take the responsibility to inform the vendors in question.
“A hacker who is not part of our community can detect a vulnerability and contact us to tell us so we can report it to the industry. It’s called coordinated vulnerability disclosure.”
But here again, there is no guarantee that the flaw will be repaired.