Franck Ebel teaches at the Maubeuge campus of the Université de Valenciennes in northwestern France. Specializing in cyber defense and computer system intrusion prevention, he tries to explain to industrialists the dangers threatening their systems. A specialist in IT security audits and monitoring management and industrial IT systems, he teaches students from across the globe how to think like a hacker in order to protect themselves from such pirates.
DirectIndustry e-magazine: Industrial material, video cameras, even hydroelectric plants—you’ve faced numerous cyber security problems.
Franck Ebel: People often forget that everything is saved on the web. It’s all “logged,” stocked and can be retrieved. Google’s an expert in that. With advanced search tools called dorks, you can identify flaws easily, find forgotten files and doorways into every system, including industrial systems.
In 2014 we could have taken control of a solar farm in the South of France, simply by typing several keywords in Google. Before the problem was corrected, we could have turned the photovoltaic panels away from the sun, cutting power to the transformers.
Using Shodan or other search engines designed to uncover flaws, I discovered that anyone could gain access to the control center of a hydroelectric plant, for example. The same type of audit tool also gave us access to industrial material from companies like Siemens and Honeywell, such as automation systems for the steel industry which could have allowed unauthorized arm transport’s handling.. Using instructions available on the web, a hacker only needs to change the operating speed of certain machines or fool around with raising the temperature of an automatic laser cutting system to block operations.
Don’t forget that the security of a business, of its production systems, also concerns its physical plant. Remote control of video surveillance cameras, temperature settings, lighting, automatic shutters and alarms are avenues of attack that are easily overlooked.
During an audit in an African seaport, we discovered how to gain access to the cameras and networking devices. None of the passwords had been modified. They were right there in the manufacturer’s instructions.
A hacker could have modified the list of containers arriving in the port. A drug dealer could have located his illegal shipment, as happened in the port of Antwerp in June 2013. Two IT experts hired by a drug cartel hacked into the Belgian port’s computers to identify the containers holding the hidden cocain.
DirectIndustry e-magazine: How do you explain this multiplication of attacks and flaws? What are the specifics of industrial cyber security?
Franck Ebel: Security is often neglected when creating industrial systems, even though they have a much longer working life than computerized management systems. In industry, an IT system can remain in place for dozens of years without being updated, without evolving. That would be unthinkable for most computers. However, we know managing updates is a real headache. You can never be sure that an update won’t block the system by creating production control software incompatibility, resulting in a shutdown and financial loss.
We still find Windows XP and 2000 being used in industry without security patches and obsolete network material whose security flaws have been known for several years. What’s more, there’s often a lack of coordination between IT managers and production managers, who are automation specialists or electronics engineers who learned to handle new developments on their own.
DirectIndustry e-magazine: What types of attacks are directed at industry?
Franck Ebel: It’s quite varied. Right now, the most common is denial of service (DoS). It consists of rendering inaccessible or inoperable a machine or other material for the duration of the attack, anywhere from a few minutes to many hours.
Ransomware is also on the increase. It penetrates and encodes a hard drive, then demands a ransom to decode it. I know of two recent cases, one where the company refused to pay, the other where the company paid. It cost them $500, a modest sum. The hard drive was decoded after payment, but the flaw that permitted the intrusion is still there. That means the company remains vulnerable.
The firm that refused to pay called on us. We didn’t try to decode the drive, which is nearly impossible at this point. Instead, we found the flaw, fixed it and restored the system using the last backup.
If they’re not changed during installation, the default passwords of networking devices is also a way into the system used by those with malicious intent.
As surprising as it may sound, attacking a factory through the computer system managing its air conditioning is also possible. Such systems are often forgotten, left off in a corner, as it were. This is a serious error, especially if it then provides access to the company’s internal network, including its production equipment.
DirectIndustry e-magazine: What countermeasures are available? Is 100% security possible?
Franck Ebel: Long-term 100% security is not possible. You can be close to 100% one day, then fall to 50% the next because an employee used a malware-infected USB drive brought in from outside. You have to consider the desired level of protection with respect to the amount of money you’re willing to spend and the risks you’re willing to accept.
A company manufacturing military aircraft doesn’t need the same level of protection as one making footballs. Nevertheless, these two economic entities are attacked for the same reasons—destruction, theft, competition. Every employee must understand the situation, from the receptionist to the president.
You also need an IT policy signed by everyone, including procedures for the use of portable storage devices. You mustn’t forget a business continuity plan and a business resumption plan, backup management, backup testing, access control for sensitive areas, etc. I believe it’s better to have an automation or electronics engineer who has evolved in the domain of IT security than a computer specialist who must learn automation or electronics. Industrialists must become aware of the dangers and begin to think about securing their systems before a human or environmental catastrophe strikes.
DirectIndustry e-magazine: Even if the number of attacks is on the rise, they’re rarely made public.
Franck Ebel: It’s not good for a company to admit it’s been attacked, not only for its image, but also because that could give others the idea that there are potential security flaws, increasing the risk of attack. In addition, knowing a hacker has broken into the system is a real cause for concern. It makes people wonder just how far the attack went. Usually, attacks are attributed to human error or computer breakdown. But the law is changing. It’s likely that the requirement to reveal successful attacks to clients will be extended to all companies, not just those of overriding importance (government services, health, energy, etc.)
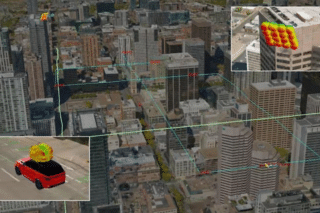
TEST YOUR SECURITY WITH SHODAN
Shodan is unusual in that it’s available via the internet. Simply put, Shodan is the Google of computer system flaw search. It’s an entirely legal tool offering targeted searches, just like the American giant. For example, searching for SCADA give you dozens of hits from all over the world, each more troubling than the next. You’d do well to test your security with Shodan. You might have some nasty surprises you’ll want to deal with right away.